With the new California Consumer Privacy Act coming into effect, companies are once again taking time to scrutinize their Information and Data Security plans, policies, and procedures. Do I have the right measures in place? Am I doing enough to protect my customers’ data? Supply chain cybersecurity is set to become an important topic for businesses this year with new regulations like the Cybersecurity Maturity Model Certification (CMMC) rolling out.
With the EU GDPR and now California’s CCPA, there’s certainly a growing trend around the regulation and protection of data, just as the risks and attacks become more significant.
Guidelines like the ones produced by the National Institute of Standards and Technology (NIST) - a government agency that develops technology, metrics, and standards - can help you understand and implement recommended security controls for information systems. In particular, there is the NIST Cybersecurity Framework which is specifically designed to help organizations better understand and improve their management of cybersecurity risk.
Extending Cybersecurity To Your Supply Chain
But it’s not just the measures within your company that need review. What about the businesses you rely on for goods and services? The supply chain could be the hidden cybersecurity risk that you haven’t yet addressed. NIST predicts that 98% of manufacturers will experience a supply chain disruption in the next two years, the majority of which will be caused by supply chain cybersecurity issues.
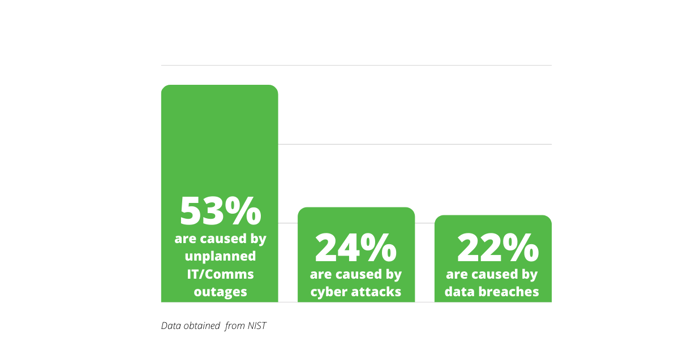
Of the supply chain disruptions that have occurred in the past few years:
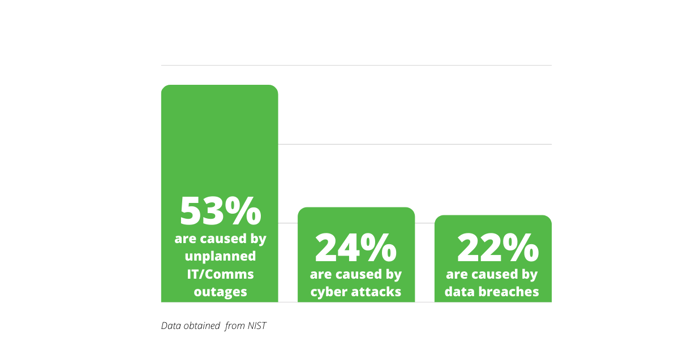
This can be a critical issue, especially considering that 55% of supply chain disruptions cost over $25 million. Companies in the aerospace and defense sector where government rules such as Defense Federal Acquisition Regulation Supplement (DFARS) require that companies meet the standard described by NIST 800-171.
The Cybersecurity Maturity Model Certification
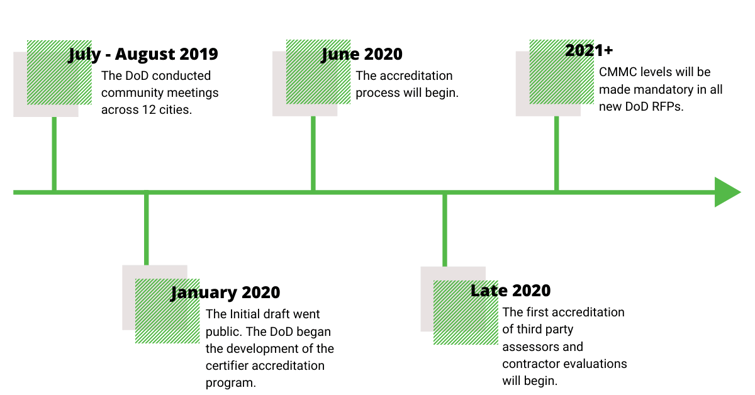
While currently adherence to these standards does not require any certification, the US Office of the Under Secretary of Defense for Acquisition & Sustainment has just released the first version of a new Cybersecurity Maturity Model Certification (CMMC). The aim of this new certification is to allow the DOD to assess and enhance the cybersecurity posture of the Defense Industrial Base (DIB).
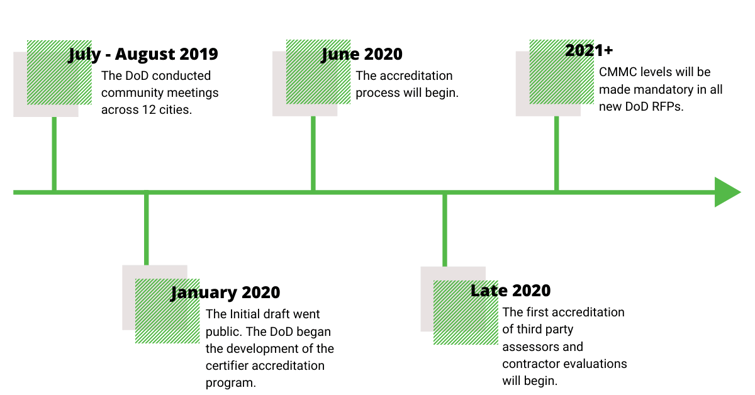
Version 1.0 of the CMMC is now available and unlike NIST SP 800-171, CMMC will implement multiple levels of cybersecurity. In addition to assessing the maturity of a company’s implementation of cybersecurity controls, the CMMC will also assess the company’s maturity/institutionalization of cybersecurity practices and processes.
Companies will have some time to evaluate the requirements of the CMMC but they will not have the option to self certify.
How to Get Started With Supply Chain Cybersecurity
If you start now, you’ll have time to properly prepare for the upcoming change. So what's the first step? A readiness assessment will let you clearly understand the cybersecurity measures, policies, and procedures your company will need to get certified. With this readiness assessment, you’ll have an action plan you can get started on right away.
The same assessment should be applied to your suppliers. Understanding your suppliers’ readiness level will help you understand the risks over which you don’t have direct control.
At Source Intelligence, we make compliance easy. By engaging 24/7, we’re able to get you the data you need without creating stress on your suppliers. Our team of global regulatory experts has over 100 years of combined experience and ensures you are compliant and up-to-date on all the latest regulations. Our platform:
-
- Centralizes your supply chain
- Automates data collection and document review
- Uses supplier intelligence to mitigate risks
- Allows you to gain internal collaboration
- Provides the tools needed to easily manage your supply chain data
- Generates dynamic reporting
See how our software takes the burden of cybersecurity compliance off your shoulders and allows you to focus on your core business functions by clicking on the button below!

![]()


.png)